Looking for Plagiarism-Free Answers for Your US, UK, Singapore, New Zealand, and Ireland College/University Assignments?
Talk to an Expert| Category | Assignment | Subject | Education |
|---|---|---|---|
| University | The Open University | Module Title | iCMA41 Assessment |
| Academic Year | 2026 |
|---|
Tries remaining: 3 Marked out of 1.00
Which three of these statements about netiquette are correct?
Select one or more:
Tries remaining: 3 Marked out of 1.00
Here is a list of glossary definitions from Part 1. The glossary is available in the Resources section of the module website.
Select the correct term from the dropdown menu to match each definition.
A term referring to any created content that is not subject to copyright.
A range of technologies used by copyright owners to control how the content they produce is used.
Using the work of others to gain some form of benefit without formally acknowledging that the work came from someone else.
A temporary fix to a bug or security problem in a particular piece of software (such as a web browser or an operating system).
Tries remaining: 3 Marked out of 1.00
Which of these statements about Good Academic Practice (GAP) are false?
Select one or more:
Tries remaining: 3 Marked out of 1.00
Drag the correct term into the appropriate space.
1. In a ransomware attack, the user is prevented from accessing their computer, e.g. bylocking the computer screen or by blocking access to computer files until money is paid.
2. This type of malicious software can easily make copies of itself, and those copies can spread via an internet connection so that the worm can consume all of a computer’s processing resources in running itself.
3. Designed to spread quickly and easily from one computer to another via internet connections and removable storage devices, the virus attaches itself to other software on your computer and activates when that software is run.
4.It appears to be innocuous software, such as a screensaver, but a Trojan may be secretly causing damage, for example, by copying personal information, such as bank details.
5. These are all forms of malware.
Tries remaining: 3 Marked out of 1.00
A random email generator is a computer program used to harvest people’s email addresses by combining common surnames with online email accounts. The general term for unsolicited emails or text messages sent to large numbers of people is spam.
Messages called hoaxes are designed to mislead people, for example, by encouraging them to spread untrue information or to delete particular files on their computers, which may cause them to crash. A particular kind of message known as phishing aims to persuade users to disclose private information such as their credit card details and PIN.
In spear phishing, clever tactics are used to target a specific individual or an organisation seeking access to sensitive informationusually for financial gain or to carry out espionage.
Tries remaining: 3 Marked out of 1.00
Choose the correct term from the list to identify the technology.
An example of a first-generation programmable computer.colossus
The microprocessor in a fourth-generation personal computer contains this cpu.
The largest type of second generation computers mainframe.
Used as switches in third generation computersic.
Used as switches in second generation computerstransistor.
Question 7
Tries remaining: 3 Marked out of 1.00
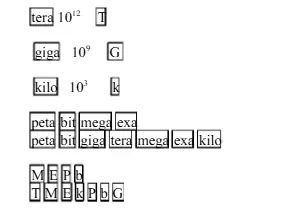
Match the prefix and the abbreviation to the power of 10.
Tries remaining: 3 Marked out of 1.00
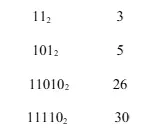
Convert the following binary numbers to their decimal equivalents.
Drop and drag the answers in the correct places:
Tries remaining: 3 Marked out of 1.00
Convert the decimal number 215 to a binary number.
Drag either 0 or 1 into the table below: 128 64 16 4 2 1
Tries remaining: 3 Marked out of 1.00
A storage device has a memory capacity of 9 megabytes (MB)
(a) How many bytes of data can be stored on this device?
Answer 1: 9437184 bytes
(b) How many bits of data is this?
Answer 2 75497472 bits
Note: You should not use scientific notation in your answers to this question. Your answers should not include spaces, commas or full-stops.
Tries remaining: 3 Marked out of 1.00
Drag and drop the correct terms into the text
Computers are designed to perform one or more specialised tasks as part of another device that might contain electrical and mechanical components. A form of computing that allows transmission of data, voice and video wirelessly across communication networks using a portable device is known as Mobile computing. An area of computer science that is interested in the development and implementation of computer technologies when they have been integrated into everyday objects and environments is called ubiquitous computing.
In cloud computing, networked remote computers are used to process and store data and run applications.
A form of ubiquitous computing, calm computing, involves technology that supports our daily activities but is more or less imperceptible.
Tries remaining: 3 Marked out of 1.00
This question relates to the Assessment guide for TM111.
(a)The University requires that you submit the written part of your assignments in a certain file format.
What is this format?
(b) To pass TM111, you need to achieve a weighted average score of 40% or more across all your assessments, and you must also achieve a threshold or minimum score on TMA03.
What is the threshold or minimum score that you must achieve on TMA03 to pass TM111?
Answer 2: Enter numbers only into the box. at least 30%
Order Custom Answer for iCMA41 Assessment
Order Non-Plagiarised AssignmentNeed expert help with your iCMA41 Assessment? We provide AI-free and plagiarism-free Assignment Help. Our team of professional writers delivers top-quality assignments that are original and crafted without AI tools, ensuring the highest academic standards. We also offer a free list of assignment samples answers, written by experts, to guide your work. Get your assignment checked with an AI and plagiarism report for complete peace of mind. Contact us today for reliable, expert assignment help UK and boost your grades!
Hire Assignment Helper Today!
Let's Book Your Work with Our Expert and Get High-Quality Content
